The release of our business whitepaper “Awareness is only the first step” was recently announced by Hewlett Packard Enterprise (HPE). The whitepaper is co-authored by HPE, UCL, and the UK government’s National Technical Authority for Information Assurance (CESG). The whitepaper emphasises how a user-centred approach to security awareness can empower employees to be the strongest link in defending their organisation. As Andrzej Kawalec, HPE’s Security Services CTO, notes in the press release:
“Users remain the first line of defense when faced with a dynamic and relentless threat environment.”
Security communication, education, and training (CET) in organisations is intended to align employee behaviour with the security goals of the organisation. Security managers conduct regular security awareness activities – familiar vehicles for awareness programmes, such as computer-based training (CBT), can cover topics such as password use, social media practices, and phishing. However, there is limited evidence to support the effectiveness or efficiency of CBT, and a lack of reliable indicators means that it is not clear if recommended security behaviour is followed in practice. If the design and delivery of CET programmes does not consider the individual, they can’t be certain of achieving the intended outcomes. As Angela Sasse comments:
“Many companies think that setting up web-based training packages are a cost-effective way of influencing staff behavior and achieving compliance, but research has provided clear evidence that this is not effective – rather, many staff resent it and suffer from ‘compliance fatigue.’”
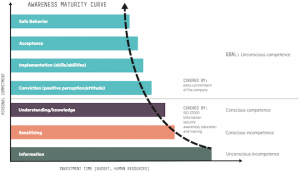
The whitepaper describes a path to guide the involvement of employees in their own security, as shown in the HPE awareness maturity curve above. To change security behaviors, a company needs to invest in the security knowledge and skills of its employees, and respond to employee needs differently at each stage.
Our empirical research explores how security and security behaviours fit within the work day, engaging directly with employees to identify the entry-points for security within a person’s work routines. Relating security to the primary role also supports dialogue with other stakeholders with competing interest in shaping the way people behave, including safety and human resources. Our research has hinted at a number of ways to engage directly with employees:
- Maintain relevance: Training should be ongoing as the organization changes and employees move into and across roles, with a focus on what is necessary for their jobs.
- Plan for learning to happen naturally: Repetition of new skills reinforces learning, but training should not overwhelm employees or take up excessive paid work time.
- Give thought to the overall package: A joined-up approach for communicating security awareness provides internal consistency.
- Share the enthusiasm: CET should be creative, fresh, and targeted to employees’ working practices, where an interactive element further involves the individual.
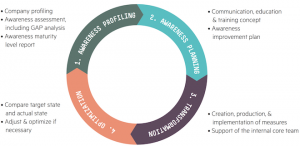
These principles inform a repeatable framework (shown above), consisting of four steps:
- A profile of awareness capabilities embodies the scope of the campaign and desired target state. Security hygiene must be followed so that recommended security behaviours can be put into practice without blocking productive activity.
- Economics-based awareness planning can remove problematic measures. There is a personal cost to changing routine behaviours; so be sure to communicate a valid reason and the benefits of changing it – treat habit change as a value proposition, not a mandate.
- A transformation phase puts security awareness initiatives into practice, where this can include activities such as security games and lunch & learn events.
- Improvements should be iterative towards reaching the target state. Optimisation can include revisiting the results of previous security hygiene exercises, where improvements should be monitored over time.
A clear view of the organisation, its culture, and interdependencies means security awareness can be targeted to specific groups of employees, delivering a set of appropriate core security skills relevant to the individual company.
The full business whitepaper can be downloaded from the Research Institute in Science of Cyber Security (RISCS) website.
There are some really smart ideas concerning security awareness training in this article. I really like how you recommend that companies continually reinforce the training through repetition. I like the idea of using an online certification class to teach the basic concepts. However, I do think it is important that employers provide their staff with new information as they move into different roles with the company.
I agree that: “It is important to understand the current security culture before trying to create a new one.”
But I’m not sure that: ” The purpose of security awareness is to achieve lasting behavioral change”. I would say that the purpose is not to recondition employees but to create (and maintain) empathy between the employee and the organisation; so that the employee can begin to appreciate the adversarial context that the organisation is operating in and to provide context for any requested behaviors. It would be interesting to study differences between compliance behaviours found in startups and large corporations.