Inadequate user interface designs in Windows 10 and macOS Mojave can cause accidental data breaches through inconsistent language, insecure default options, and unclear or incomprehensible information. Users could accidentally leak sensitive personal data. Data controllers in companies might be unknowingly non-compliant with the GDPR’s legal obligations for data erasure.
At the upcoming Annual Privacy Forum 2019 in Rome, I will be presenting the results of a recent study conducted with my colleague Mark Warner, exploring the inadequate design of user interfaces (UI) as a contributing factor in accidental data breaches from USB memory sticks. The paper titled “Fight to be Forgotten: Exploring the Efficacy of Data Erasure in Popular Operating Systems” will be published in the conference proceedings at a later date but the accepted version is available now.
Privacy and security risks from decommissioned memory chips
The process of decommissioning memory chips (e.g. USB sticks, hard drives, and memory cards) can create risks for data protection. Researchers have repeatedly found sensitive data on devices they acquired from second-hand markets. Sometimes this data was from the previous owners, other times from third persons. In some cases, highly sensitive data from vulnerable people were found, e.g. Jones et al. found videos of children at a high school in the UK on a second-hand USB stick.
Data found this way had frequently been deleted but not erased, creating the risk that any tech-savvy future owner could access it using legally available, free to download software (e.g., FTK Imager Lite 3.4.3.3). Findings from these studies also indicate the previous owners’ intentions to erase these files and prevent future access by unauthorised individuals, and their failure to sufficiently do so. Moreover, these risks likely extend from the second-hand market to recycled memory chips – a practice encouraged under Directive 2012/19/EU on ‘waste electrical and electronic equipment’.
The implications for data security and data protection are substantial. End-users and companies alike could accidentally cause breaches of sensitive personal data of themselves or their customers. The protection of personal data is enshrined in Article 8 of the Charter of Fundamental Rights of the European Union, and the General Data Protection Regulation (GDPR) lays down rules and regulation for the protection of this fundamental right. For example, data processors could find themselves inadvertently in violation of Article 17 GDPR Right to Erasure (‘right to be forgotten’) despite their best intentions if they failed to erase a customer’s personal data – independent of whether that data was breached or not.
Seemingly minor design choices, the potential for major implications
The indication that people might fail to properly erase files from storage, despite their apparent intention to do so, is a strong sign of system failure. We know since more than twenty years that unintentional failure of users at a task “is often caused by the way in which [these] mechanisms are implemented, and users’ lack of knowledge”. In our case, these mechanisms are – for most users – the UI of Windows and macOS. When investigating these mechanisms, we found seemingly minor design choices that might facilitate unintentional data breaches. A few examples are shown below and are expanded upon in the full publication of our work.
A number of the issues that we identified likely stem from a conflict between the colloquial use of linguistically similar terms ‘delete’ and ‘erase’, and their very different technical meaning. In simplified terms – although the details vary based on technical nuances such as the type of memory chip and file system used – ‘delete’ is an operation in which the OS simply forgets the existence of a file, while the ‘erase’ operation actively removes the file from the system, e.g. by overwriting or flashing the binary storage. Thus, ‘deleted’ files usually remain on the memory chip until overwritten by coincidence, whereas ‘erased’ files are typically impossible to recover.
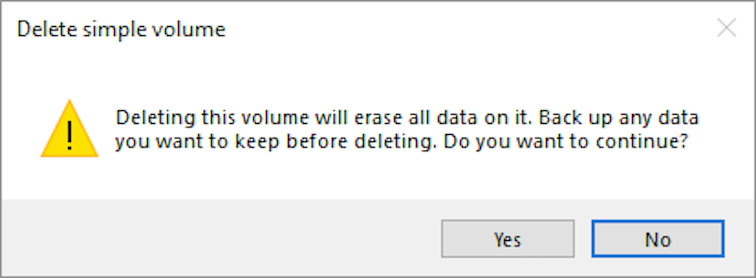
Inconsistent language within the UI of an OS, such as when deleting files from Trash in macOS 10.14 shown in Figure 1, can foster the misunderstanding that the terms ‘erase’ and ‘delete’ would denote the same technical function. A lack of sufficient guidance and cues is also evident in the screenshots shown in Figure 1. For example, users could be better supported in their decision making by elaborating on the expression that they “can’t undo this action”, e.g. by adding a reference to possible data recovery through forensic analysis software.
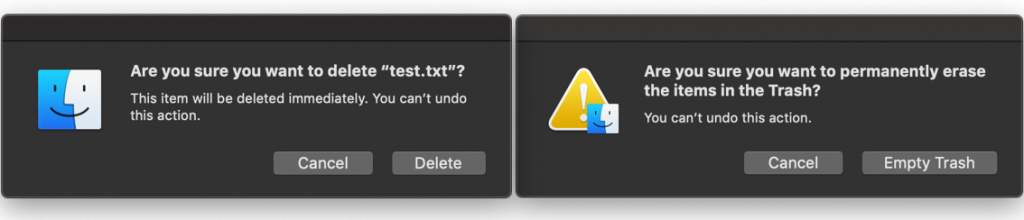
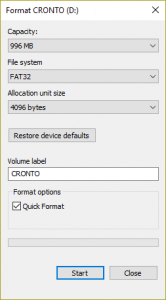
Users commonly understand default options as a recommendation, reducing the likelihood of other options being selected. This effect is reinforced when a description text for this option is omitted, such as in case of the pre-selected Quick Format option in Windows 10 shown in Figure 2. The alternative could be to require users to make an active selection before they can proceed and to provide description texts for the available options.
I don’t want to be misunderstood as blaming or shaming the original designers of these UIs for their work. As I have said before, the evaluation of any design is always context-dependent. The design choices for the UI of delete and erase operations in Windows and macOS might have been okay at the time of their original design, but as circumstances around these designs have evolved (e.g., new legislation, new data recovery techniques and free to download software, etc.) they should be reconsidered. An important lesson we can (re-)learn from this is that designs need to be re-evaluated not only when they’re changed but also when their context changes.
The way forward
As mentioned earlier, we know since more than twenty years that users’ unintentional failure at a task “is often caused by the way in which [these] mechanisms are implemented, and users’ lack of knowledge”. Reworking the UI of Windows and macOS to improve these mechanisms is one side of the coin, the other is addressing the users’ lack of knowledge.
Our paper presents a number of alternative designs, but further research is suggested to identify further shortcomings in the existing UI around deletion functionality and to implement and evaluate alternative designs. Perhaps equally important is the reconsidering of the language used to denote technical operations, and to seek alternatives to the linguistically similar terms ‘delete’ and ‘erase’.
For the latter, to improve the users’ knowledge, we see the national Data Protection Authorities and the European Data Protection Board (and their international counterparts, where existing) being best positioned to create official guidance on how to erase data using popular OS and/or open source software.
This work has received funding from the European Union’s Horizon 2020 research and innovation programme under the Marie Skłodowska-Curie grant agreement No 675730.